Appearance
Vulnerability discovery
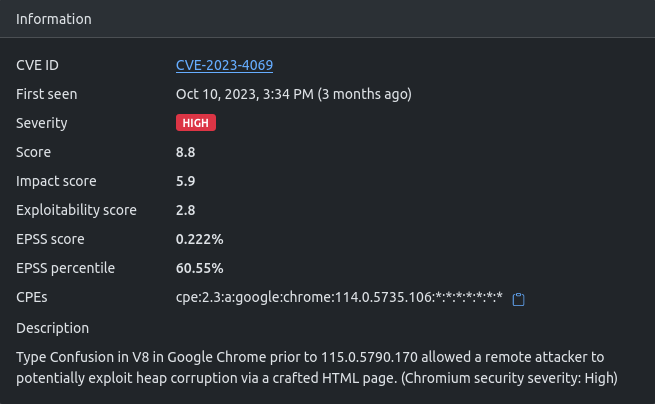
In addition to asset inventory and management, Enclave also provides vulnerability discovery. Enclave uses the National Vulnerability Database (NVD) as well platform based security trackers (Windows, Ubuntu, RedHat, Debian). Scanning takes place one a day per asset and covers both OS and select software vulnerabilities.
Please contact us to enable vulnerability discovery for your organization.
How it works?
- Our agent sends OS, package and software information up to the EMC.
- Once a day, scans are built and run for each asset.
- If the scan information has changed since the last scan, the scan is saved and new vulnerabilities are displayed in the EMC.
- Old vulnerabilities are marked as fixed if they are no longer present in the scan.
Adding exceptions
You create vulnerabilty exceptions to ignore specific vulnerabilities for a group of tagged assets. This can be useful if you have a group of assets that you know are not vulnerable to a specific CVE or if you've accepted risk of a CVE. You can add exceptions in the Exceptions view under Assets Management.
Ignoring CVEs
You can ignore CVEs by clicking the ignore button on the vulnerability. Ignored vulnerabilities will not be displayed in the EMC. You can view ignored vulnerabilities by filtering them in the Vulnerability Explorer by ignored. Please note that when ignoring CVEs, it will take until the next scan time for the vulnerability to be removed as active in software and dashboards. It will be immediately be ignored from the asset iteself.
FAQs
What sources are used for vulnerability discovery?
We use the following sources for vulnerability discovery:
- NVD: National Vulnerability Database
- Microsoft: Microsoft Security Tracker
- Ubuntu: Ubuntu Security Tracker
- RedHat: RedHat Security Tracker
- Debian: Debian Security Tracker
How often are vulnerabilities synced?
We run scans on asset once per day. The scan information is saved and compared to the previous scan. If there are new vulnerabilities, they are displayed in the EMC. You can manually rerun a scan from an asset in the EMC if needed.
Acknowledgements
- NVD: This product uses the NVD API but is not endorsed or certified by the NVD.
- EPSS: See EPSS at https://www.first.org/epss

